【要点】
◎Emotetを使用するサイバー犯罪組織
【目次】
概要
【辞書】
◆MUMMY SPIDER (Malpedia)
https://malpedia.caad.fkie.fraunhofer.de/actor/mummy_spider
【別名】
| 別名 | 命名組織 |
|---|---|
| TA542 | Proofpoint |
| Mummy Spider | CrowdStrike |
| Gold Crestwood | |
| TEMP.Mixmaster | |
| UNC3443 |
【概要】
- Emotet を使った攻撃を展開
【最新情報】
◆Alert (AA22-110A) Russian State-Sponsored and Criminal Cyber Threats to Critical Infrastructure (CISA, 2022/05/09)
[重要インフラに対するロシアの国家的・犯罪的なサイバー脅威]
https://www.cisa.gov/uscert/ncas/alerts/aa22-110a
⇒ https://malware-log.hatenablog.com/entry/2022/05/09/000000_2
記事
【ニュース】
◆TA542 Returns With Emotet: What's Different Now (DarkReading, 2020/08/28 13:05)
[TA542はEmotetで復活。今回、何が違うのか]Researchers report the TA542 threat group has made code changes to its malware and started targeting new locations with Emotet.
[研究者の報告によると、TA542脅威グループはマルウェアのコードを変更し、Emotetを使って新しい場所をターゲットにし始めました]https://www.darkreading.com/threat-intelligence/ta542-returns-with-emotet-whats-different-now/d/d-id/1338785
⇒ https://malware-log.hatenablog.com/entry/2020/08/28/000000_5
【ブログ】
◆Deep Analysis of New Emotet Variant – Part 1 (Fortinet, 2017/05/03)
https://www.fortinet.com/blog/threat-research/deep-analysis-of-new-emotet-variant-part-1.html
⇒ https://malware-log.hatenablog.com/entry/2017/05/03/000000_3
◆EMOTET Returns, Starts Spreading via Spam Botnet (Trendmicro, 2017/09/07 09:10)
https://blog.trendmicro.com/trendlabs-security-intelligence/emotet-returns-starts-spreading-via-spam-botnet/
⇒ https://malware-log.hatenablog.com/entry/2017/05/03/000000_3
◆Meet CrowdStrike’s Adversary of the Month for February: MUMMY SPIDER (CrowdStrike, 2018/02/08)
https://www.crowdstrike.com/blog/meet-crowdstrikes-adversary-of-the-month-for-february-mummy-spider/
⇒ https://malware-log.hatenablog.com/entry/2018/02/08/000000_3
◆Threat Actor Profile: TA542, From Banker to Malware Distribution Service (Proofpoint, 2019/05/15)
https://www.proofpoint.com/us/threat-insight/post/threat-actor-profile-ta542-banker-malware-distribution-service
⇒ https://malware-log.hatenablog.com/entry/2019/05/15/000000_18
◆日本ではURLZoneがトップマルウェアに また、EmotetとLINEフィッシングも拡大 (Proofpoint, 2019/06/19)
https://www.proofpoint.com/jp/threat-insight/post/urlzone-top-malware-japan-while-emotet-and-line-phishing-round-out-landscape-0
⇒ https://malware-log.hatenablog.com/entry/2019/06/19/000000_8
◆A Comprehensive Look at Emotet’s Summer 2020 Return (Proofpoint, 2020/08/28)
[エモテットの2020年夏の復帰を総合的に見てみる]
https://www.proofpoint.com/us/blog/threat-insight/comprehensive-look-emotets-summer-2020-return
⇒ https://malware-log.hatenablog.com/entry/2020/08/28/000000_6
【公開情報】
◆Alert (AA22-110A) Russian State-Sponsored and Criminal Cyber Threats to Critical Infrastructure (CISA, 2022/05/09)
[重要インフラに対するロシアの国家的・犯罪的なサイバー脅威]
https://www.cisa.gov/uscert/ncas/alerts/aa22-110a
⇒ https://malware-log.hatenablog.com/entry/2022/05/09/000000_2
【図表】

Indexed volume of email messages containing Emotet, TA542’s signature payload (from 5/1/17-5/1/19)

Timeline of major milestones in TA542 activity
出典: https://hackernews.blog/2019/05/15/threat-actor-profile-ta542-from-banker-to-malware-distribution-service/

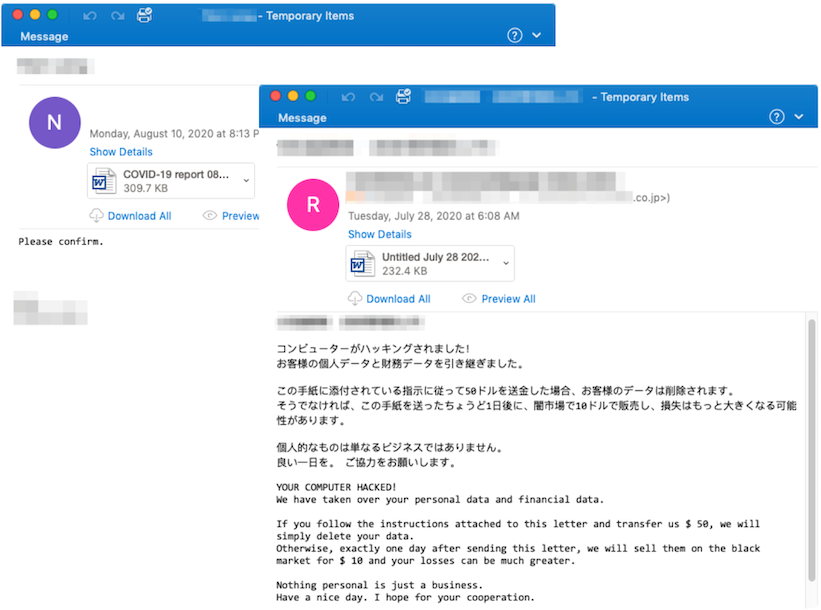
出典: https://www.proofpoint.com/us/blog/threat-insight/comprehensive-look-emotets-summer-2020-return
【検索】
google: TA542
google: Mummy Spider
google:news: TA542
google:news: Mummy Spider
google: site:virustotal.com TA542
google: site:virustotal.com Mummy Spider
google: site:github.com TA542
google: site:github.com Mummy Spider
■Bing
https://www.bing.com/search?q=TA542
https://www.bing.com/search?q=Mummy%20Spider
https://www.bing.com/news/search?q=TA542
https://www.bing.com/news/search?q=Mummy%20Spider
https://twitter.com/search?q=%23TA542
https://twitter.com/search?q=%23Mummy%20Spider
https://twitter.com/hashtag/TA542
https://twitter.com/hashtag/Mummy%20Spider
関連情報
【関連まとめ記事】
◆サイバー犯罪組織 (まとめ)
https://malware-log.hatenablog.com/entry/Cybercrime